The crack works by exploiting vulnerabilities in the software’s code, allowing users to bypass the password or key protection. This can be done through various methods, including patching the software, using a keygen, or employing a crack tool. Once the crack is applied, users can access protected files without any restrictions.
\[ x=5 \]
USB Copy Protection 6.10 is a software designed to protect files and folders from unauthorized copying or access. It was widely used by individuals and organizations to secure their sensitive data, especially when sharing files via USB drives. The software worked by creating a virtual drive that could be used to store protected files, which could only be accessed with a specific password or key. Usb Copy Protection 6.10 Crack
\[ y=10 \]
\[y = x +5 \]
In the world of digital security, copy protection has become a crucial aspect of safeguarding intellectual property. One such software that gained popularity in the past was USB Copy Protection 6.10. However, with the emergence of cracks and bypass methods, the software’s effectiveness has been compromised. In this article, we’ll delve into the world of USB Copy Protection 6.10, explore the crack, and discuss its implications.
The Rise and Fall of USB Copy Protection 6.10: Understanding the Crack and Its Implications** The crack works by exploiting vulnerabilities in the
In conclusion, while the USB Copy Protection 6.10 Crack may have seemed like a solution to bypass security measures, it is essential to prioritize data security and explore alternative solutions that do not compromise confidentiality, integrity, and availability.
The USB Copy Protection 6.10 Crack may seem like a convenient solution for accessing protected files, but it poses significant risks to data security and integrity. Instead of using cracked software, individuals and organizations should prioritize robust security measures to protect their sensitive information. By doing so, they can ensure the confidentiality, integrity, and availability of their data. \[ x=5 \] USB Copy Protection 6
In today’s digital age, data security is a significant concern. With the rise of cybercrime and data breaches, protecting sensitive information has become a top priority. Copy protection software like USB Copy Protection 6.10 was designed to address this need. By encrypting files and folders, users could ensure that their data remained confidential, even when shared with others.
However, as with any software, the security of USB Copy Protection 6.10 was eventually breached. A crack, which is a hacked version of the software, emerged, allowing users to bypass the protection and access protected files without a password or key. The crack, often searched for using keywords like “Usb Copy Protection 6.10 Crack,” became popular among individuals who wanted to access protected files without authorization.
始于口碑
连接线生产经验
行业成功案例
作为国内首批涉足电脑周边产品的专业制造商,自1999年以来,Z-TEK坚持以自主研发、生产、外贸、OEM/ODM于一体的完整性及规范化的运营模式,产品具备独特的外观、新颖的结构、严谨的工艺、优良的品质、健全的测试认证,树立高新电子产品的前端地位。
未来, Z-TEK 将持续保持产品的竟争力和先进性,矢志成为高端线缆制品消费引导者。对产品积极创新,精益求精,对用户竭诚尽责,坚持不懈。
“专业成就品牌,敬业铸造精品,服务赢得信赖。”Z-TEK时刻恪守自己的承诺,携手广大客户共创美好未来。


自1998年苹果首次将USB作为iMac连接外部设备的标准接口之后,USB就逐渐开始被各家企业所接受,并广泛应用于电脑、手机、相机、游戏机等各类电子产品中。就在本...
查看详情
第一点:需要注意各种材料的情况和质量根据技术指标等特点分析可知,数据线的编织方法和相应的铝箔层对数据线本身会起到良好的防护和屏蔽作用,想要让这种usb...
查看详情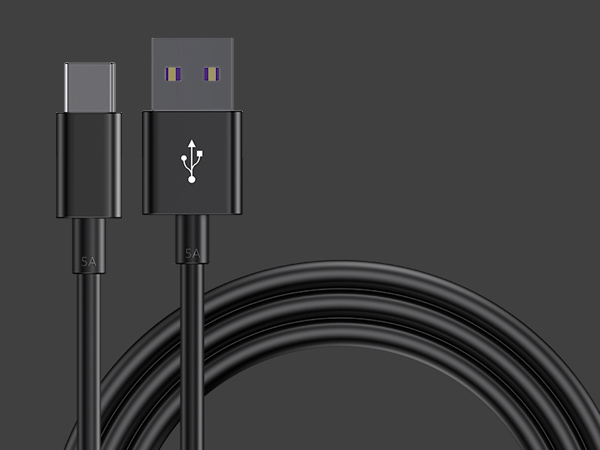
1、数据线插拔次数达到或超过设计次数。早期USB接口插拔设计寿命为几百次,现在能够达到几千次。接口容易出现的问题就是插头簧片接触不良,所以充不进电。如果...
查看详情